Today’s trend of being “always on”, fully mobile and connected has led to the significantly increased use of mobile devices such as notebooks and personal digital assistants. Personal storage devices such as flash drives have become universal business tools in an effort to maintain productivity when out of the office. First marketed in 2000, 85 million USB flash drives were sold in 2007.
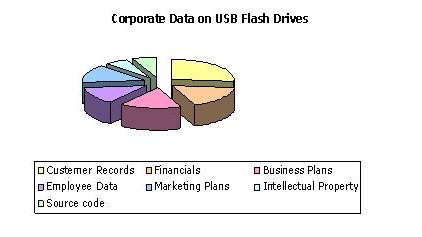
And yet these mobile devices often lack security control - 80-90% of USB flash drives sold to business last year were not encrypted – are not stored in a secure location and used without limitation. Despite the fact that they might contain private data, financial information, business plans or other confidential records, ENISA warns that USB flash drives are usually overlooked by corporate policies on audits, back-ups, encryption and asset management.
Often devices are inadvertently lost such as when the UK Revenue and Customs misplaced an unencrypted CD-ROM with the personal details of 25 million taxpayers. In a Datamonitor survey of 1,400 ICT professionals, 60% revealed they had experienced a ‘data leak’, 61% of which believed it to be the work of insiders. More often than not, criminals seek out flash drives as their theft usually goes unreported due to their small size and low cost.
The Executive Director of ENISA, Mr Andrea Pirotti commented: “The cost of a USB flash drive may be insignificant but the value of the data it might contain can be priceless. ENISA strongly encourages companies with highly regulated or sensitive data to better manage the use of ‘plug-and-play’ devices. But equally all organisations should establish a first line of defence by increasing awareness of the risks and available safeguards. Data loss is not just a security concern for the IT department but a strategic issue with far-reaching implications for a firm’s future.”
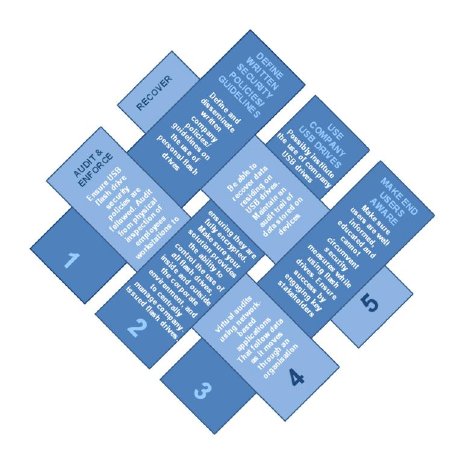
Among its 19 recommendations, the Agency specifically highlights the importance of a risk assessment to understand the costs of data leakage and the controls needed to offset this threat. Companies also need to introduce security policies for these devices and consider authentication and encryption tools.
The full report is available at: http://www.enisa.europa.eu/...