The Red Hat ISV Partner Program has been instrumental in the growth of certified applications. We encourage the combination of open source and traditional technologies to strengthen the fabric of enterprise computing in order to provide technology solutions that give our customers more choice. Software vendors with applications certified on Red Hat Enterprise Linux are invited to join the program here.
Clearly, applications are critical. Nobody buys Red Hat Enterprise Linux just to admire. Customers want the largest choice possible, while applications vendors (ISVs) want to make their products available on the most popular platform. These two considerations work closely together to create a powerful positive feedback loop based around Red Hat Enterprise Linux. Another success factor relies on the API/ABI (application programming/binary interface) stability that is an important element of every Red Hat Enterprise Linux release. By keeping interfaces rock-solid for the life of each release, ISVs do not need to keep re-certifying their products and customers do not need to keep installing updates to keep them running. In the rapidly changing open source world, this is particularly valuable.
Also, because all members of the Red Hat Hat Enterprise Linux product family share a common core - kernel, development tool-chain, libraries, etc. - our ISV partners only need to certify their software once for a single architecture. Certify once, deploy anywhere. In other words, when our partners certify their products on Red Hat Enterprise Linux for x86, it will work on Red Hat Enterprise Linux Advanced Platform for Intel x86. This simplifies life for ISVs and customers.
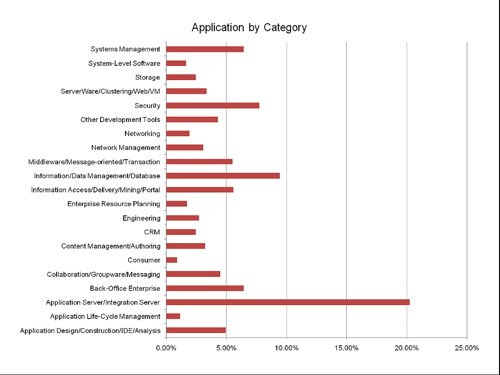
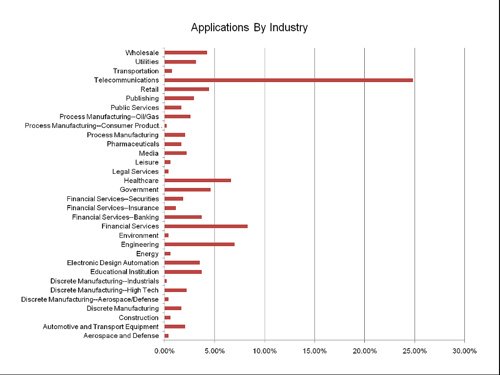
Of course, counting how many applications are certified turns out to be more complicated than you might imagine. And maybe it doesn’t even matter because, where applications are concerned, there’s a classic 80:20 rule in play. In other words 80 percent of customers use the same 20 percent of applications. Provided the 15 applications you need are available the fact that there are several thousand to choose from doesn’t really matter. Nevertheless, it’s fun to count. There are many places to look. First off, we include many core applications as part of Red Hat Enterprise Linux itself, such as Apache, Tomcat, Samba, MySQL and many network services. Then, there are the applications that our ISV partners certify and formally include in our ISV catalog. This catalog passed the 3,000 mark in the last quarter. It provides applications in 20 categories, covering more than two dozen industries. Lastly, there are the applications that the ISV, for one reason or another, has not added to our online catalog. We know that this is a large category, so it always makes sense to check directly with an ISV if the application you need is not in our catalog.
The growth rate of applications in our catalog has been astonishingly rapid, from just a 100 or so applications in late 2002, we crossed the 1,000 barrier in 2004, and the 2,000 barrier in early 2006.
Keeping Applications Secure: The SELinux Partner Program We’ve just begun the new SELinux (Security Enhanced Linux) Partner Program, available to our ISV partners to help them create security policies so that their applications are as secure as possible.
SELinux technology was built in collaboration with major security vendors and the U.S. Government’s National Security Agency (NSA) and is included as a core component of Red Hat Enterprise Linux along with a number of policy writing and debugging tools. We think that the security provided by SELinux is a key differentiator for customers and ISVs when compared to the security capabilities of other operating systems. Under this program, the customer receives an application with enhanced security provided by SELinux – the result is that the application is tightly controlled so that it cannot perform actions that are outside of how it normally functions, even when taken over by an attacker. With the SELinux Partner Program, ISVs work in partnership with Red Hat to develop this capability for their applications.
Certified Application Categories
Currently, our certified applications fall into more than 20 categories. Here’s a breakdown of our five largest application categories:
Application Server/Integration Server: 20% of certified applications
Information Data/Data Management/Database: 10% of certified applications
Security: 8% of certified applications
Back-office Enterprise: 6% of certified applications Systems Management: 6% of certified applications
Industry Applications
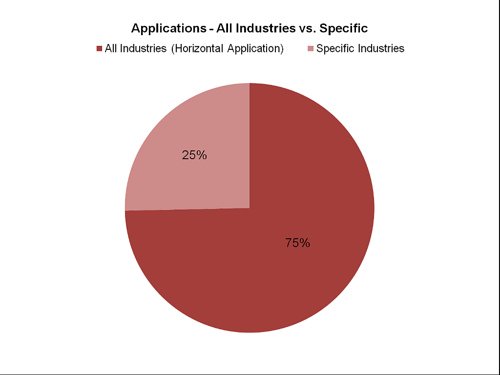
Almost 75 percent of the ISV applications in the Software Catalog are used by virtually all industries, with specific industry applications geared toward industries including telecommunications, financial services, engineering, healthcare, government and more.