Key benefits for all companies using IBM Lotus Notes/Sametime 8.x
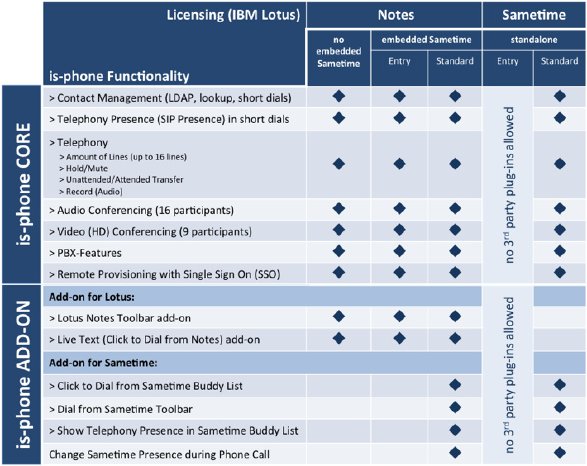
- Cost savings due to no licensing upgrade and changes in the IT/telecom eco-system Users running Lotus Notes client with embedded
Sametime - Entry or Standard versions - or Notes client without Sametime are allowed, from a IBM licensing perspective, to run is-phone for Lotus in their environment at no additional Lotus licensing costs.
In addition, is-phone for Lotus is agnostic with most SIP-enabled platforms in the back-end (Aastra, Alcatel, Avaya/Nortel, Broadsoft, Cisco, Genesys, Metaswitch, Siemens) as well as media servers like Polycom or Tandberg, allowing IT/telecom departments important CAPEX and OPEX cost savings (up to 75%).
- Faster UC adoption at no risk
is-phone for Lotus Notes/Sametime client applications can be freely evaluated by IT/telecom departments or hosted service providers in their production environment and validate use cases and UC features in days, just requiring SIP account credentials for test. Once validated, IT/telecom administrators or service providers can quickly start the roll-out phase in a fully automated way by using the remote provisioning mechanism embedded in is-phone client, either synced with Lotus Notes or IP PBX administration tools.