These are some of the results of a recent study conducted by InfoCom surveying nearly 100 operators — spread among 40 countries worldwide — about security options currently avail-able for SME customers.
About a third of carriers worldwide offer security solutions on a standalone basis only. These may include PC or Internet security software, cloud-based solutions — for instance, cloud-based Unified Threat Management, Security-as-a-Service — and managed security services. Only about 10% of operators worldwide do not offer any security solution, either standalone or bundled.
The tendency to bundle basic security options is strong in the Americas, particularly in key economic markets such as Canada and the US but also in emerging markets such as Argentina, Brazil, Colombia, Mexico and Uruguay: in these countries the incumbents and al least the main alternative operator offer basic security options for SMEs, bundled with a broadband access. The same strategy is followed by carriers in Eastern and Western Europe. In the Asia Pacific region, on the contrary, the trend is leaning towards standalone security offers. In some markets in Southeast Asia, operators also do not offer any standalone security solution and rather direct customers to other kind of providers, for instance IT companies. In the Middle East, the marketplace is more differentiated, with some incumbents, for instance STC in Saudi Arabia and Etisalat in the United Arab Emirates (UAE), offering bundled security options, while the main alternative carriers provide standalone offers only.
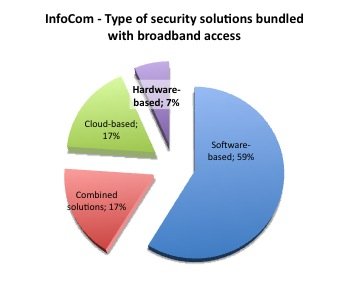
The most common security solution adopted by SME customers worldwide is software-based with basic features based on software of ESET, F-Secure, McAfee, Symantec and Trend Micro. F-Secure and McAfee are, by far, the most popular choices with McAfee being dominant in North America and Latin America, while F-Secure has a stronger foothold among providers in the Asia Pacific, Eastern Europe and Western Europe.
The study revealed also an interesting emerging trend regarding the bundling of security cloud-based features as a value-added service for FTTH and other top-tiered/high revenue-generation broadband offers (e.g. FTTC/VDSL). This is the strategy, for instance, followed by SingTel that, while it still offers ADSL to SME customers, markets its FTTH services intensively with cloud-based security features as part of its USP.
About this extract: These are some of the results of a recent study conducted by InfoCom surveying nearly 100 operators — spread among 40 countries worldwide — about security options currently avail-able for SME customers. This study focuses on security options offered with broadband connections using ADSL (including ADSL2 and ADSL2+), SDSL/SHDSL, FTTC/VDSL and FTTH/FTTB as security breaches and surveillance activities are often occurring at network access level or are based on the Internet be-haviour —including personal information shared through social networking and location-based ser-vices. If you are interested to know more, do not hesitate to get in contact with us. Talk to us. We listen.