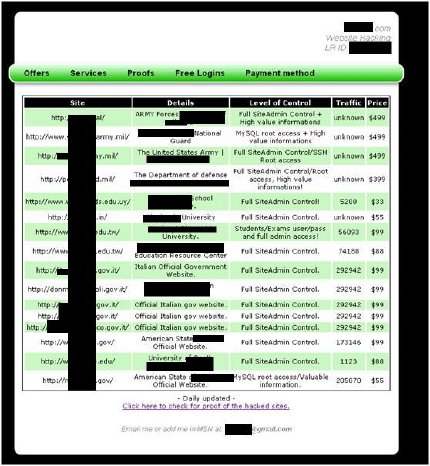
- The list includes (with original hacker's typos)
The 'traffic' probably stands for the number of records within the Database tables. The 'goods' in this case are probably the needed information for the 'Level of Control.' For 'full site admin' - probably the credentials and the URL of site administrator interface.
- The hacker is also selling personally identifiable information (PII) from hacked sites, for $20 per 1K records
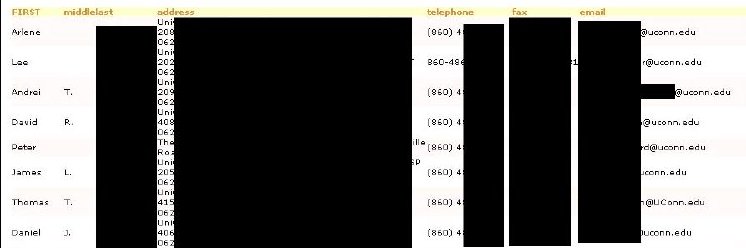
- For example, here they want to sell a list of UConn staff
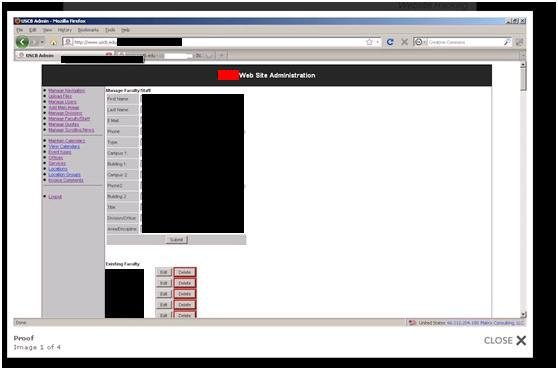
- In the screenshot below, the hacker tries to show proof of accessing the administrator interface for a major university
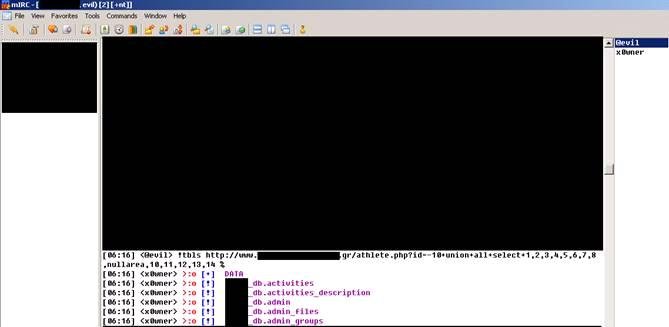
- The victims' vulnerabilities were probably obtained by SQL injection vulnerability automatic scanner and exploited in automatic manner, as the hacker published his methods in a post in some hacker forum - see screen shot and explanation
In the screen shot above we can see IRC "chat" between the SQLi "master" = @evil which issues the scanning commands and the exploiting "x0wner" which performs the commands. In this specific case @evil issues command for to x0wner to obtain DB tables names ("!tbls") from vulnerable link ("www.site.gr/athlete.php?id=...") x0wner reports its findings - the tables "activities","admin",...